Live Life King Size!
Tutorial
-
How to connect digi Portserver TS8 to Cisco console
⏱︎
Read time:
1–2 minutesRead More →: How to connect digi Portserver TS8 to Cisco consoleIf you are here in search of the pinout for connecting a Cisco device using console port to the PortServer TS8 then you are at the right spot. First, how to reset it to factory settings: > The reset button…
-
DHCP snooping not working – multiple switches in path
⏱︎
Read time:
1–2 minutes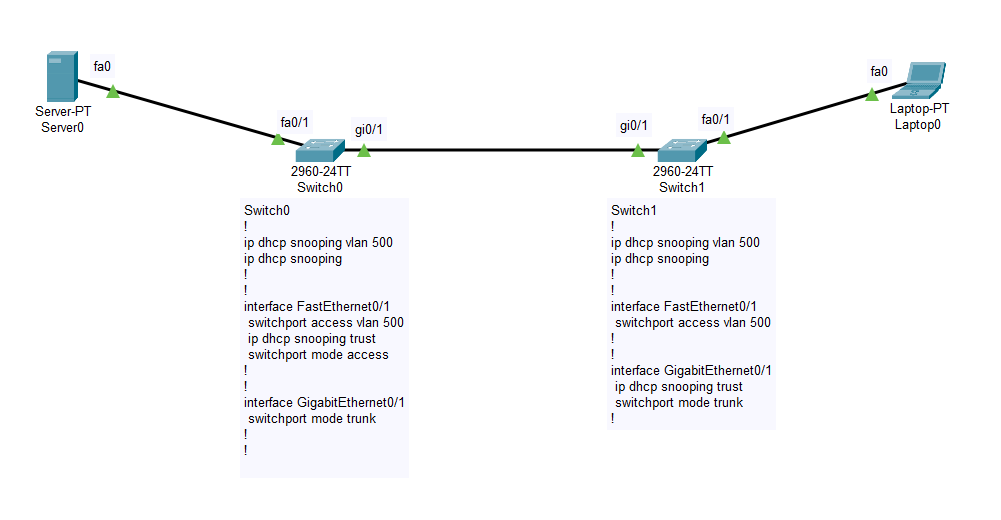 Read More →: DHCP snooping not working – multiple switches in path
Read More →: DHCP snooping not working – multiple switches in pathLets look at this topology. The Server0 is configured with DHCP service and then it is connected to the Switch0 on port Fa0/1. This switch is connected to Switch1 from port Gi0/1 to Gi0/1. The laptop which is a DHCP…
-
ACME DNS-01 basic Autorenewing Script for txt records on dns.he.net
⏱︎
Read time:
2–3 minutes Read More →: ACME DNS-01 basic Autorenewing Script for txt records on dns.he.net
Read More →: ACME DNS-01 basic Autorenewing Script for txt records on dns.he.netOptions are limited when you want to generate a free Let’s Encrypt SSL certificate using WIN-ACME and you can not or do not want to publish verification files on the server – especially if you want the certificates to be…
-
How utilize SSH tunnel for any remote service
⏱︎
Read time:
1–2 minutesRead More →: How utilize SSH tunnel for any remote serviceThis is something Advanced level so if you are a beginner, try to follow along and I will try to explain it in the easiest to understand way. Why do we need SSH tunneling? Well, for me it makes it…
-
How to setup a lightweight Linux (Ubuntu) based SSH server
⏱︎
Read time:
1–2 minutesRead More →: How to setup a lightweight Linux (Ubuntu) based SSH serverThis is not a beginner level process so if you do not know why you would need an SSH server, this post is not for you. Now that is out of the way, let’s begin: Grab ISO for ubuntu server…
-
[How To] Create Bootable Windows XP USB
⏱︎
Read time:
1–2 minutesRead More →: [How To] Create Bootable Windows XP USBYesterday I ran into trouble while trying to install Windows XP on an old computer. The problem? Well I didn’t have a CD ROM drive on that computer and the only way to install was to use a bootable USB.…
